In an interview with the Wall Street Journal, a convicted thief, Aaron Johnson, currently serving up to eight years in the Minnesota Correctional Facility, has shed light on his methods of tricking iPhone owners into revealing their passcodes and subsequently pilfering their life savings. This revelation comes in the wake of Apple’s introduction of Stolen Device Protection, raising concerns about the ongoing vulnerabilities of iPhones.
Johnson, motivated by financial desperation while experiencing homelessness and the responsibilities of parenthood, candidly shared his journey into theft when faced with limited job opportunities. “I’m already serving time. I just feel like I should try to be on the other end of things and try to help people,” he expressed during the interview.
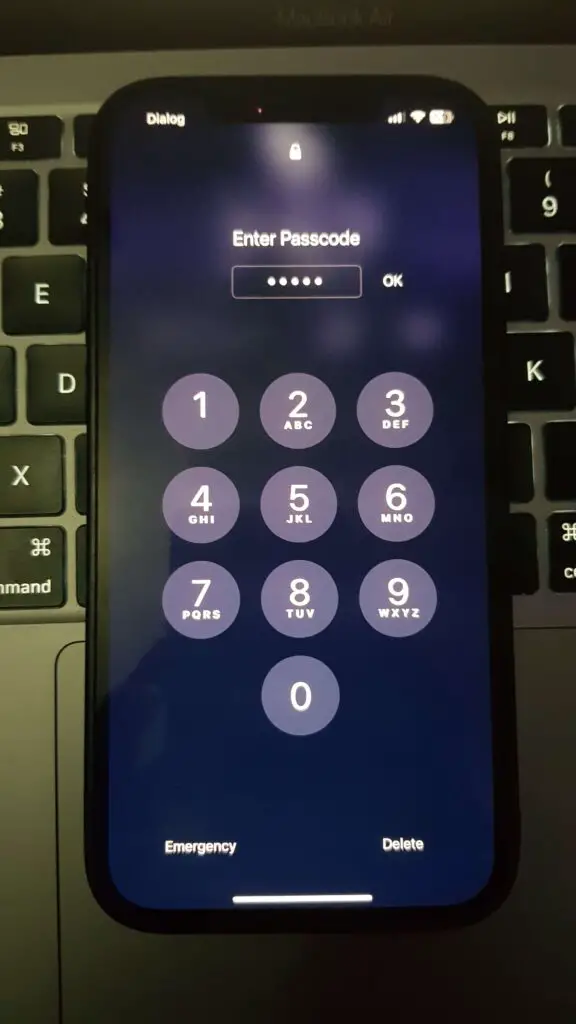
Explaining his transition into stealing iPhones, particularly favouring higher-value models, Johnson highlighted the pivotal role of passcodes in granting him extensive access to the devices. Despite the advancements in technology, his insights underscore the persistent susceptibility of iPhones to theft, prompting a call for increased awareness among iPhone owners regarding safeguarding their devices and personal information.
“The passcode is like a double-edged sword,” he remarked. “It could be a savior at times—or it could be a menace.”
In the dimly lit atmosphere of late-night bars, Aaron Johnson divulges his strategy, noting a preference for targeting college-aged men due to their perceived vulnerability while inebriated. According to him, women tended to be more vigilant, whereas men were “already drunk and don’t know what’s going on for real.”
Engaging them in conversation, Johnson employed various tactics, from offering substances to posing as a rapper eager to connect on Snapchat. The unsuspecting victim would willingly hand over their iPhone, anticipating a quick exchange. Johnson would inquire about the passcode, to which the reply was often something like ‘2-3-4-5-6,’ a sequence he would memorize.
Once in possession of the iPhone and its passcode, Johnson swiftly altered the Apple ID password, disabling the Find My iPhone feature. He emphasized the importance of speed in this process, likening it to “beating the mice to the cheese.”
With the device secured and his face added to Face ID, Johnson delved into the iPhone’s contents, seeking notes or photos containing additional password details, including those for bank accounts. Overnight, he exploited these accounts, siphoning funds, and subsequently used Apple Pay to make purchases at various stores.
This systematic approach allowed Johnson to steal as many as 30 iPhones in a single weekend, raking in $20,000 from goods purchased and phones sold. His ventures reportedly amounted to a staggering $300,000, although he contests this figure, estimating the actual haul to be between $1 million and $2 million.
Notably, all of these activities occurred before the introduction of Apple’s Stolen Device Protection. While acknowledging the value of this feature, Johnson underscores the primary preventive measure: “Don’t give your passcode out.”
What is Stolen Device Protection for iPhone, and how does it enhance security?
In response to instances where criminals have employed tactics to obtain users’ passcodes before stealing iPhones, Apple is introducing a robust security measure in the upcoming iOS 17.3, aptly named “Stolen Device Protection.”
Here’s an overview of what this security feature entails and how it functions.
Stolen Device Protection in a Nutshell
According to Apple’s beta notes, Stolen Device Protection serves as an additional layer of security in the unlikely event that someone steals your iPhone and gains access to your passcode. The key features of this security measure include:
1. Biometric Authentication for Saved Passwords:
– Accessing saved passwords requires Face/Touch ID to ensure the user’s identity.
2. Security Delay for Sensitive Settings:
– Changing critical settings, such as the Apple ID password, is safeguarded by a security delay.
3. Location-Based Convenience:
– No delay is imposed when the iPhone is in familiar locations, such as home and work.
Stolen Device Protection acts as a deterrent against a thief who possesses both the stolen device and knowledge of the victim’s passcode. It prevents them from executing essential device and Apple ID account operations, such as altering the device or Apple ID passcode, by mandating biometric authentication with no passcode fallback.
The authentication process varies, with some operations requiring a single biometric verification, while others necessitate the user to wait for an hour before authenticating a second time using Face ID or Touch ID.
The overarching goal is to introduce an additional obstacle that complicates unauthorized access, data erasure, or the resetting of the device to factory settings for resale. Stolen Device Protection aims to bolster the security of iPhones, making it more challenging for thieves to compromise user data and device integrity.